Early on in the troubleshooting process for Internet connectivity issues, make sure that any relevant application ports are open.
Using the well-known Telnet command is a simple way to accomplish this without installing any additional software.
Describe Telnet
A virtual terminal connection is used by the network protocol telnet to offer bidirectional interactive text-oriented interactions on the Internet or in Local Area Networks .[1]
To check if the path from our machine to the server is open over that port, we can use the Telnet command to connect to a port on a distant server.
Telnet was initially developed to allow remote terminals to manage and control mainframe machines.
Because Telnet sends data in plain text, other secure remote control protocols have mostly supplanted it.
How Does Telnet Function?
Through a connection to a virtual terminal, the Telnet protocol establishes a communication link. With the help of Telnet control information and the transmission control protocol, the data is distributed in-band (TCP).
When establishing a connection on port 23, Telnet offers a log-in screen and permits logging in as the real user of the remote device, unlike other TCP/IP protocols. Direct control is granted together with all of the same rights as the credentials’ holder with this form of access.
Windows’ command prompt provides access to the Telnet command. Additionally, the telnet command is available for Linux and macOS.
Related
How to Test Open Ports Using Telnet in Windows
To check open ports, use the following Telnet syntax:
Telnet “address,” “port,”
Addresses can be either symbolic or numerical when using the command. For instance:
towel.blinkenlights.nl telnet 23
As an alternative:
telnet 80 127.0.0.1
One of the following three outcomes occurs after executing the command:
1. An error is thrown by the command, indicating that the port is not open for connections:
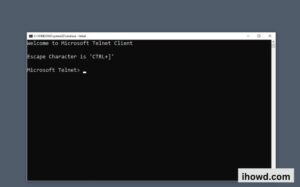
2. The command results in a blank screen, which shows that the port is open.
3. The screen of the telnet host is displayed when the command is run on an open port 23, indicating that a Telnet connection has been established.
Security
Telnet is an insecure, unencrypted protocol. Anyone who keeps an eye on a user’s connection can read their plaintext username, password, and other secret information entered during a Telnet session. With this knowledge, access to the user’s device is possible.
Protocols associated to SSH

Some contemporary systems only permit command-line access via a virtual private network (VPN) or utilising Secure Shell (SSH), an encrypted tool comparable to Telnet (VPN). Many professional groups demand the usage of SSH, PuTTy, or other solutions instead than Telnet due to security concerns. The main reason SSH is preferred over other alternatives is that it encrypts all data travelling across the communication connection.
Additionally, unlike more recent protocols, Telnet does not allow graphical user interfaces (GUIs), rendering it incompatible with a wide range of contemporary applications, including word processors, spreadsheets, and web browsers. Large amounts of data, especially visual data, would be lost through a Telnet session connection since those systems operate intricate graphical interfaces.
